It’s always a bit of an eye opening experience to see just how much the bad guys are trying to attack your website.
I’ve been reading a fair amount about the security of WordPress sites lately. Enough to be fairly worried about whether I was doing enough to protect the sites I administer.
I didn’t think I was doing enough. So I installed a new (to me) free plug-in, Better WP Security, after reading its positive reviews, seeing its popularity, and understanding that the plug-in is routinely updated. (Those factors, by the way, are generally good factors to consider when selecting WordPress plugins) A few hours after intalling, I read the logs produced by the plug-in. Yikes!
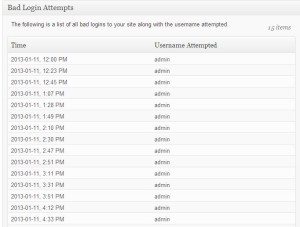
Here’s one:
WordPress “admin” user name hack
One can see pretty clearly that somebody or somebodies were trying to get into my site using the user name “admin”. Why is that?
“Admin” is a default user name. If it’s not still the WordPress default user name, many people simply use it out of force of habit (probably with the password “password” or “123”.
If you do that, you are leaving the keys to your WordPress website at the front door. Actually, you’re leaving the front door open and have posted a sign that says “Bad Guys: Please come in!”
Best practice: eliminate the user name “admin” from your site.
After enough attempts in prompt succession, the plug-in will lock out the IP address from which the attempts are coming. Interestingly, these attempts did not produce a lock out. This suggests either that multiple people (more likely, computers) were trying to gain access using “admin”, or the same person or network was using different computers (or spoofing IP addresses).
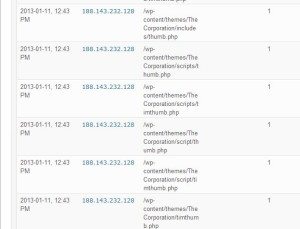
Timthumb.php or thumb.php exploit
The malicious traffic that did generate the lock out (and a permanent ban from me) was an attempt to exploit the timthumb.php and thumb.php files. Some themes use one or another of these files. Outdated version of the file are not secure. (Details of the exploit here).
 I use ElegantThemes premium themes. Hats off to them for not using these files (at least in the themes I use)!
I use ElegantThemes premium themes. Hats off to them for not using these files (at least in the themes I use)!
How do I know? I installed the Timthumb Vulnerability Scanner plug-in (chosen again because of popularity, ratings, and updates) and scanned all my sites. No such file to be exploited.
Because the IP address has now been banned, the hacker can’t access the site from the Russian IP address (flagged in the beginning of this post).
WordPress website security is essential; plug-ins can help
No security solution is fail safe. There will always be trade-offs between security and convenience.
Nevertheless, if you want to take some steps to reasonably protect your WordPress site from the bad guys, there are some fairly simple, essential steps you must take. Installing and configuring a few reliable, free plug-ins is a good step to take. There are always more.